Welcome to the virtual location of the KUKU Trust. 🙂
In the real world our site is the city of Dar es Salaam at the East African coast. The name “Dar es Salaam” has Arabic roots and means “haven of peace”. And indeed: I have hardly met more friendly and humble people anywhere else.
“Kuku”, a word of their Kiswahili language, is the unisex name for poultry. Eating is a popular activity around here and kuku the favourite dish of the most. 😉
In our case though, KUKU is the abbreviation of “Kompyuta ya Umma Kiswahili Uhuru”. Kompyuta ya Umma is “the people’s computer”. Uhuru means freedom. Uhuru is also our name for an operating system in Kiswahili language. KUKU outlines the objective of our activity:
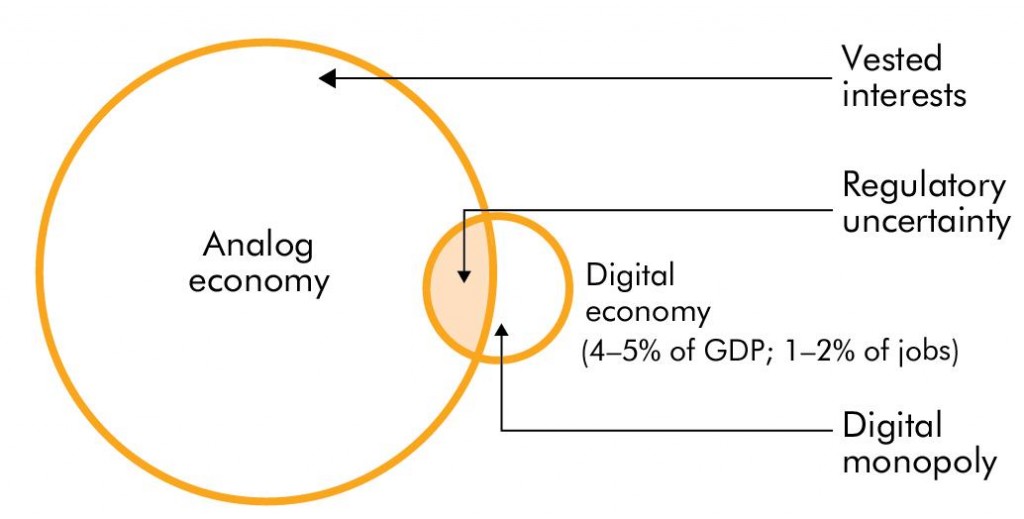
Helping Tanzania to overcome the Digital Divide by her own means
“You never change things by fighting the existing reality. To change something, build a new model that makes the existing model obsolete.”
Richard Buckminster Fuller
[codepeople-post-map]