“… we are opposed around the world by a monolithic and ruthless conspiracy that relies primarily on covert means for expanding its sphere of influence—on infiltration instead of invasion, on subversion instead of elections, on intimidation instead of free choice, on guerrillas by night instead of armies by day.
It is a system which has conscripted vast human and material resources into the building of a tightly knit, highly efficient machine that combines military, diplomatic, intelligence, economic, scientific and political operations.”
– John F. Kennedy, 35th US-President, April 27, 1961
A mysterious affair
While the true circumstances forcing Bolivians President Morales’ plane to land in Vienna, Austria might never be revealed, it definitely was a great demonstration of that “tightly knit, highly efficient machine” in action.
On 03/07/2013 the Head Of State was on his way home from a Moscow energy conference, when out of the blue in the late evening the NATO states Italy, France, Spain and Portugal closed their airspace for the presidential jet. As a result an emergency landing at Vienna airport followed and 13 hours of enforced stopover for His Excellency and his delegation.

VIENNA | Wed Jul 3, 2013 5:50am EDT
(Reuters) – No unauthorized people were found on board Bolivian President Evo Morales’ government plane at Vienna airport when Austrian authorities carried out a voluntary inspection, Deputy Chancellor Michael Spindelegger said on Wednesday.
Looking at the picture of a tired and angry Head Of State, accompanied by the Austrian President, giving a press conference in the middle of the night, 2 ideas might enter your mind:
- An amazingly unconstrained atmosphere – obviously Morales is not a member of the untouchable superclass.
- Which power subjects the plane of the elected head of a sovereign state to a check for “unauthorised people”?
A president and a spy
President Morales happened to be in Moscow at the same time as Edward Snowden1, the man who made public, that the USA are carrying out exactly this “covert conspiracy” their President Kennedy had warned about, by keeping the entire global electronic communication under surveillance.
But even more terrifying than the existence of such a system per se, is the ruthlessness, by which the perpetrators defend their global control system: “All Law is Gone: Naked Power Remains“.
Extra Legality
Indeed here is striking evidence of the Mafia Principle2 at work, which Professor Chomsky defines as the underlying, determining force in foreign affairs – and Snowden is a key witness:
“This willingness by powerful states to act extra-legally represents a threat to all of us, and must not be allowed to succeed.”
– Edward Snowden, NSA whistle-blower3
Legal, Like East Germany
In order to assess this threat, let us compare the US National Security Agency (NSA) with the widely considered as the most effective and repressive intelligence and secret police agency in the world – the former East German State Security (Stasi):
“I became an expert on East Germany, which was then the ultimate surveillance state. Their secret police were monstrously efficient: they had a huge paper-based system that held information on virtually everyone in the country – a population of about 16-17 million. The Stasi’s motto was “to know everything”.”
– Thomas Drake, former senior executive of the NSA
Stasi versus NSA4
Below you find a visualisation by OpenDataCity, comparing5 the space the filing cabinets of the Stasi and the NSA would use up, if the NSA would print out their 5 Zettabytes:
Global supranational Stasi
Drake recalls that at the time he worked with the NSA, the then Director General Michael Hayden set as target: “We need to own the net.” Today it is evident that the entire Information and Communication Technology (ICT) has been rigged to function as a global surveillance machine.
Within the next decade Big Business expects to reap US$14.4 trillion from the internet users. This goldmine has to be guarded against competition on taxpayers’ expense by an intelligence community budget of US$52.6 billion alone for fiscal year 2013.
No loose ends
There is too much money at stake to allow some Third World country Head of State to possibly protect an insider who needs to explain to the world that the entirety of ICT became a cornerstone of a “monolithic and ruthless conspiracy” of the kind President Kennedy warned about.
Making the Internet become profitable
The basic idea behind getting rich and influential is depicted on every backside of the United States One Dollar Bill: the many must be focussed on the few on top, who collect and manage their money and information.

Accordingly the most certain way to make money with the Internet is by establishing a pyramid scheme like Facebook. By design though, the network contains the code to ultimate freedom in connectivity: it requires neither a centralised governance in either technological implementation nor policies for access and usage; each constituent network sets its own policies.
[ws_table id=”1″]
Only the implementation of a virtual map, predominately designed by US-corporations6 channels the common interest into mainstream habits and rites, preselecting ideas and desires for the masses – and making alternatives hard to find. After all the hidden force which pulls the strings behind the curtain on the global stage of the World Wide Web is software code.
Disrupting the current Internet paradigm
The prove that above said isn’t just a (conspiracy-) theory but a fact, is affirmed by our Crown’s witness – Microsoft Inc.! Just 10 years ago their researchers promoted a very different idea about how the Information Society should develop:
“Community-based multi-hop wireless networks is disruptive to the current broadband Internet access paradigm […] It is important because it allows free flow of information without any moderation or selective rate control. Compared to the large DSL and cable modem systems that are centrally managed, mesh networking is organic — everyone in the neighborhood contributes network resources and cooperates.”
Self Organizing Wireless Mesh Networks7
The researchers saw “many advantages to enabling such connectivity and forming a community mesh network”. It’s worth to highlight their findings – and compare with today’s reality:
- “Share faster, cost-effective Internet access via gateways that are distributed in their neighborhood” – today a graduated pricing scheme, limits individual Internet usage by amount of data and/or time, driving up the price for connectivity.
- “Another advantage is that neighbors can cooperatively deploy backup technology and never have to worry about losing information due to a catastrophic disk failure” – today corporations have implemented cloud storing system like Skydrive, Google Drive, scavenging all users’ data for resale opportunities.
- “A third advantage is that this technology allows bits created locally to be used locally without having to go through a service provider and the Internet.” – This means nothing less than that local communities could communicate free of charge! At the same time the worst nightmare for the NSA would materialise, as the efforts to monitor billions of community networks would even exceed their bloated budget by far. Not to mention that all citizens could encrypt all data traffic.
Commonwealth through shared resources
In the future probably two networks will complement one another: Besides the connection to the Internet (blue) – “The Cloud” – a free and open neighbourhood network will spread out (red). Sharing their resources all participants benefit from communication free of charge! Consequently such a communal network increases social interaction – inclusive interactive education – builds up a community support structure, strengthens the local economy, and altogether improves the general well being of community residents.
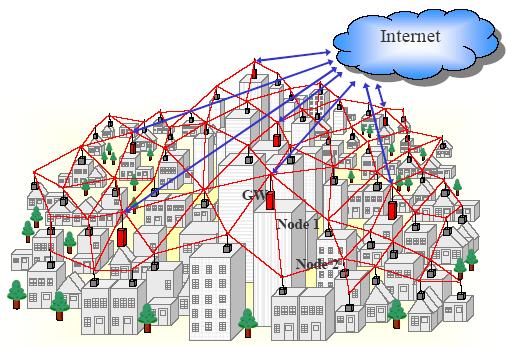
A free society needs a free and open communication network, with transparent control mechanisms, democratically legitimised. Consequently a Mesh Connectivity software – unfortunately discontinued by Microsoft – is an essential component of our Uhuru IT-tookit.
News update:
On 31/08/2013 the Washington Post confirmes, that “U.S. spy agencies” abuse on global scale the “Internet as a theater of spying, sabotage and war”. The US-government resorts to the same methods criminal hackers are using – even collaborating with them by:-
- Covertly implanting malicious software which turns computer into dormant “zombies“, prepared to follow remote commands.
- Projecting to control at least 85,000 implants in strategically chosen “targets” around the world by the end of 2013. On the push of a button such zombies instantly recruit armies of “robots” (other computers in the network), transforming specific sectors of the Internet into a remote controlled “botnet“.
News update: As the New York Times reports, the NSA controls even computer which are not connected to the Internet. In 2010 the NYT had withheld these details, at the request of American intelligence officials, when it reported about United States / Israel cyberattacks on Iran with the worm “Stuxnet”.
A German newsmagazine, published the N.S.A.’s catalog of hardware products that can secretly transmit and receive digital signals from computers, a program called ANT.
The Washington Post also reports about rising tensions between the USA and Brazil united with Mexico, as suspicion substantiates, that Brazilian President Dilma Rousseff, and Mexican President of Mexico, Enrique Peña Nieto are targets of U.S. electronic communication espionage.
“A grave breach of trust between allies” (Update 26/10/2013):
“If leaders are targeted, it’s probably not by accident, but systematic and out of principle,” said an editorial in the German newspaper Die Welt, after it became evident that the NSA might have eavesdropped on German Chancellor Merkel’s private mobile phone already since 2002! Nowadays routinely a large variety of electronic warfare operations is conducted out of US-embassies and -consulates around the world by a highly classified Special Collection Service unit (SCS).
German journalists recently investigated an occurrence in the 1980ies when a US-spy passed a more than 4000 pages strong “National Sigint Requirement List” (NSRL) to the East German secret service. This NSRL proves that a US surveillance authorisation does not pertain to the individual, but the political post – in other words: since at least 25 years the US routinely spy on all foreign political or economic decision makers they can get hold of.
Computing platforms8 are the weakest links
The French newspaper L’Express has published a memo, which it claims originates from French prime minister’s office. Among many other directives, it recommends that French cabinet ministers stop using smartphones because they are not secure.
Breaking News 23 June 2015:
WikiLeaks is publishing “Espionnage Élysée“, a collection of reports and documents on the US National Security Agency. According to these TOP SECRET dossiers, the last 3 French Presidents Francois Hollande (2012–present), Nicolas Sarkozy (2007–2012), and Jacques Chirac (1995–2007), as well as French cabinet ministers and the French Ambassador to the United States have been direct targets of NSA surveillance.
[The NSA] “has moved more to compromising platforms and hardware, instead of trying to break more sophisticated encryption schemes”.
“That is why it is so important that we inform people that their platforms are the weakest link.”
– US encryption expert Mike Janke
As a matter of fact the weakest link should be given the most attention. Hence it follows that the safest solution for Tanzanians will be to rely on the national Uhuru OS platform. The Uhuru OS code will be always open for perusal by the public, therewith constituting a ideal foundation for setting up protective measures:
“Encryption works. Properly implemented strong crypto systems are one of the few things that you can rely on.”
– NSA whistleblower Edward Snowden
“NSA infected 50,000 computer networks with malicious software” (Update 23/11/2013)
The objective of the NSA is the “mastery of the global network” with the capability to target “anyone, anytime, anywhere”, as documented by their top-secret “SIGINT Strategy 2012–2016“.
According to an article published by The New York Times on 16/02/2016, the United States military develops Cyberattack plans “for all kinds of possible conflicts” with other countries. This confirms, that the Stuxnet computer worm that destroyed centrifuges inside Iran’s Natanz uranium enrichment site was only one element of a much larger US-prepared cyberattack plan, named “Nitro Zeus“, that targeted Iran’s air defenses, communications systems, and key parts of its power grid.
Definitely cyberwarfare has become a standard element of the U.S. arsenal for what are now called “hybrid” conflicts. Thereby “short of a full-scale war” acts of sabotage are performed, “to prepare the battlefield” by crippling as much computer-managed infrastructure as possible — not only military but also civilian!
“[…] collateral damage is always hard to predict. It is easier to turn off power grids, for example, than to start them up again”.
What If Snowden Was on Board the Bolivian President’s Jet?
UNASUR Declaration in Emergency Session following the diversion of Evo Morales’ plane in Europe
– Lecture by Noam Chomsky, at Boston University, March 17, 2009
“Individuals have international duties which transcend the national obligations of obedience. Therefore individual citizens have the duty to violate domestic laws to prevent crimes against peace and humanity from occurring.“
In contrast to the Stasi, the NSA can count on new technologies and can therefore collect information in gigantic quantities. To get the picture, we compared the data volume in this little app:
According to a report by the NPR, the data center of the NSA in Utah will be capable of saving 5 Zettabytes (5 billion Terabyte). Assuming that a filing cabinet with 60 files (30.000 pages of paper) uses up 0,4 m², which would correspond to 120 MB of data, the printed out Utah data center would use up 17 million square kilometers. Thereby the NSA can capture 1 billion times more data than the Stasi!